Tuesday, 30 July 2024
Explain elliptic curve cryptography algorithm in detail with example step by step ?
Elliptic Curve Cryptography Algorithm : in detail with example step by step explanation is as follows.
Monday, 29 July 2024
What is Elliptic Curve Cryptography? Part 1 Basics Knowledge required about Elliptic Curve in detail with 10 Questions
What is Elliptic Curve Cryptography?
Part 1: Basics Knowledge required about Elliptic Curve in detail with 10 questions.
Before studying the Elliptic Curve Cryptography We must have knowledge of following Basic Things:
Those are as follows:
1. What is an Elliptic Curve?
2. What Kind of x and y values are going to be used to form Elliptic Curve?
3. Which type of curve is going to be used in Elliptic Curve Cryptography?
4. What is finite field?
5. How to construct Elliptic Curve over a Finite Field Z/11?
6. What are the Characteristics of Elliptic Curve?
7. How to Compute addition of Two different points P and Q on elliptic curve i:e P + Q = R ?
7. How to Compute addition of same points P with P on elliptic curve i:e P+P = 2P ?
Sunday, 28 July 2024
What is Asymmetric Key Cryptography and also explain the detailed working of Asymmetric Key Cryptography?
What is Asymmetric Key Cryptography and also explain the detailed working of Asymmetric Key Cryptography?
After reading the above notes you are able to answer the following questions?
1. What is Asymmetric key in cryptography?
2. What is the difference between Symmetric Key and Asymmetric Key Cryptography?
3. Explain in detail the working of Asymmetric Key Cryptography?
4. How to encrypt and decrypt the message using Public Key Cryptography?
5. How many asymmetric keys will be required if four devices are connected with each other in network?
UGC NET question on Symmetric Key Cryptography: consider if four devices are connected with each other then how many keys are needed ?
UGC NET Question on Symmetric Key Cryptography: Consider if four devices are connected with each other then how many symmetric keys are needed ?
Example:
Take your own example and try to solve it by referring above notes: consider there are 7 devices are connected with each other so how many symmetric keys are needed?
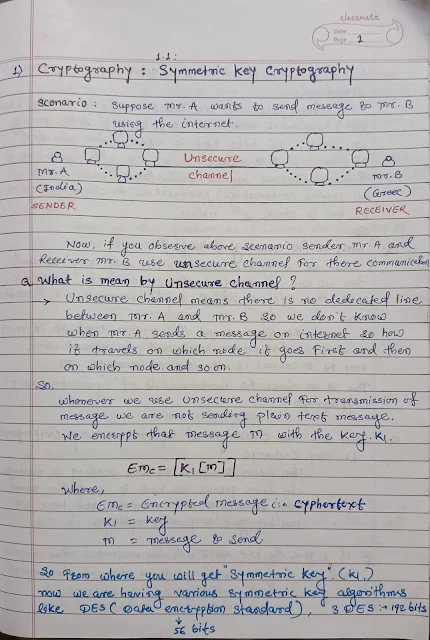
What is Symmetric Key Cryptography? What are the Challenges in symmetric key cryptography?
Symmetric Key Cryptography:
After reading the above contents you are able to answer following questions.
1. What is mean by unsecure channel?
2. What is Symmetric Key?
(Symmetric Key means same Key used for both Encryption & Decryption)
3. What are the various Symmetric key algorithm?
4. What is the meaning of Key?
5. How Symmetric key Cryptography works explain with example?
6. What are the challenges of symmetric key cryptography?
Subscribe to:
Comments (Atom)


























.jpg)